tiCrypt
End-to-End Encrypted Compute Environments
tiCrypt is a product of Tera Insights and the University of Florida Research Computing. It is a single, fully integrated platform for regulated workloads designed to exceed NIST 800-171/CMMC Level 2 requirements.
Is tiCrypt a Good Fit for Your Organization?
A simple four-point check to help determine whether tiCrypt aligns with your compliance, infrastructure, and deployment needs.
Fit & alignment
Four Questions
Does your organization handle regulated workflows (e.g., NIST SP 800-171/172, CMMC Level 2 or 3, ITAR)?
Are your workflows dependent on software outside Microsoft 365 that cannot run in GCC High?
Does your organization have the scale and resources to operate an on-premises secure environment?
Is your organization based in the United States or Canada?
Alignment Score
Begin by answering each question.The score indicates whether your organization aligns with the conditions tiCrypt is designed to support.
No responses are stored, logged, or transmitted. Processed locally within your session.
tiCrypt Core Features
Core features include a secure Vault for file storage and sharing, controlled access to virtual machines via RDP and terminal sessions, and integrated administrative tools for managing users, permissions, and system activity.
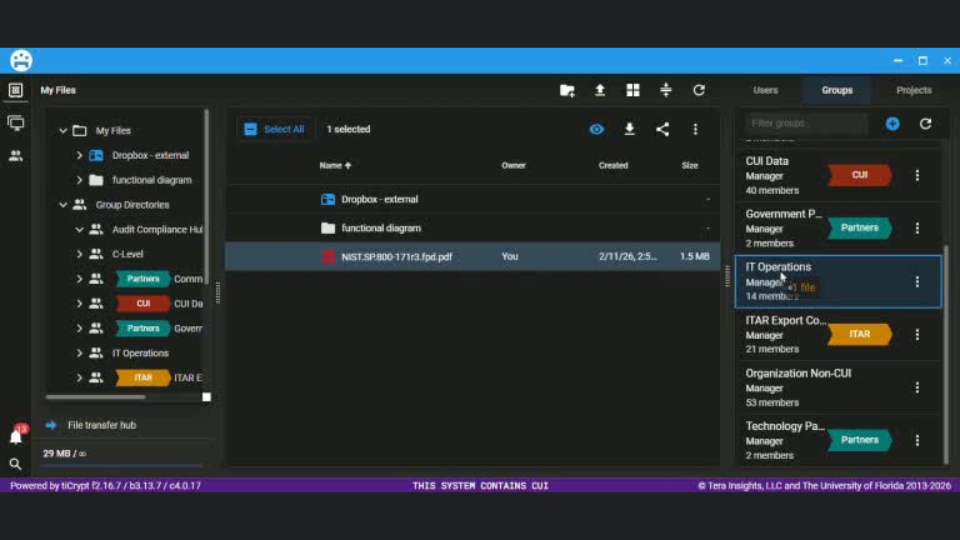
Secure Storage & Sharing
tiCrypt Vault provides an end-to-end encrypted space for storing and organizing files and folders.
Files and folders can be shared across projects and groups with clear permissions, and data can be securely received from outside the enclave via controlled dropboxes or SFTP.
Access
VM & Terminal Access
tiCrypt provides controlled access to secure environments through both terminal (SSH) and full desktop (RDP) interfaces, allowing users to interact with systems without exposing sensitive data outside the enclave.
Access to virtual machines and mounted drives can be securely shared, enabling collaborative use within groups. When explicitly permitted, virtual machines can also connect to one another, supporting complex workflows while preserving isolation, auditability, and strict access control boundaries.
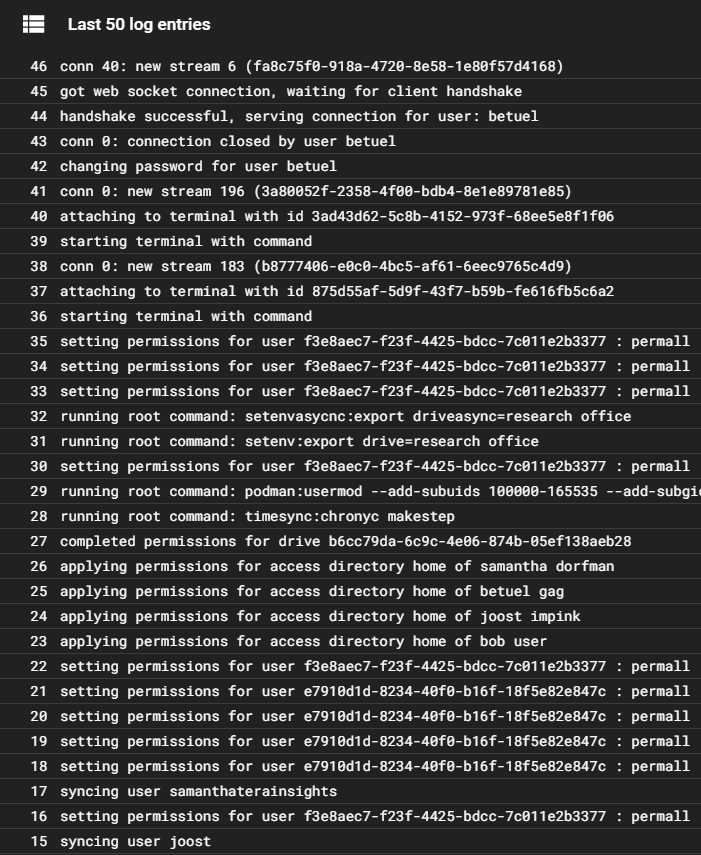
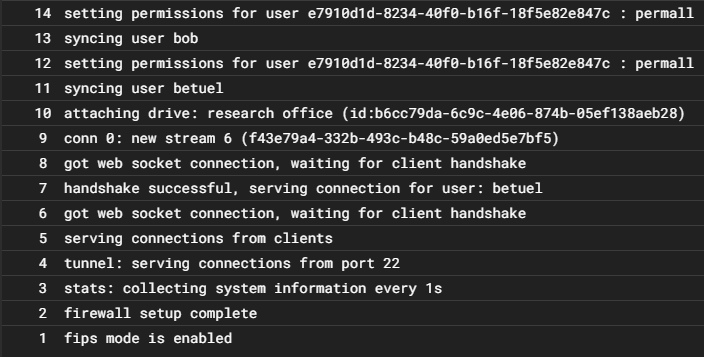
Full System Logging
tiCrypt provides administrators and authorized teams with complete, structured visibility across the entire system from the moment environments are created. Every action is recorded to support operational oversight, audit readiness, troubleshooting, and security review.
From access events to system-level and infrastructure behaviors, tiCrypt maintains a continuous, tamper-resistant history that ensures accountability and traceability for sensitive workloads from day one.
Permissions
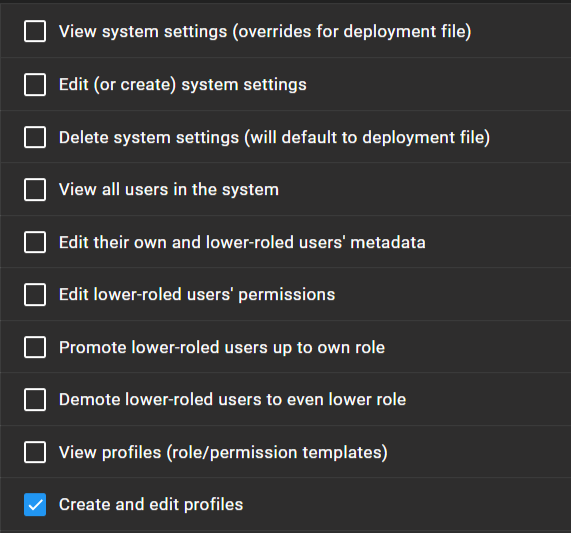
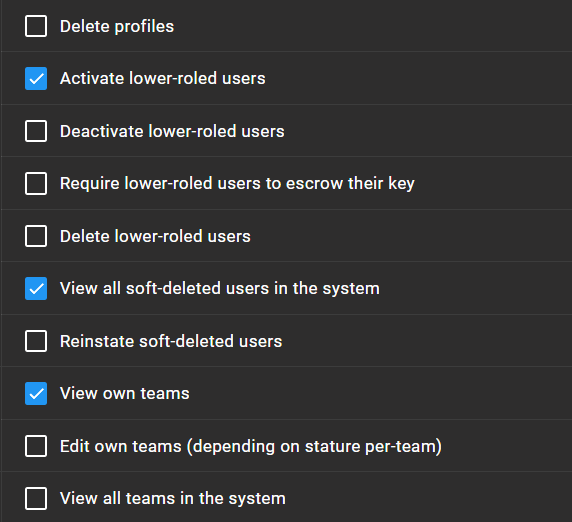
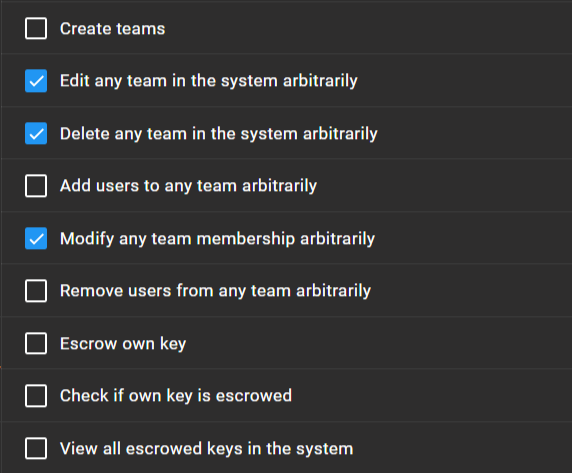
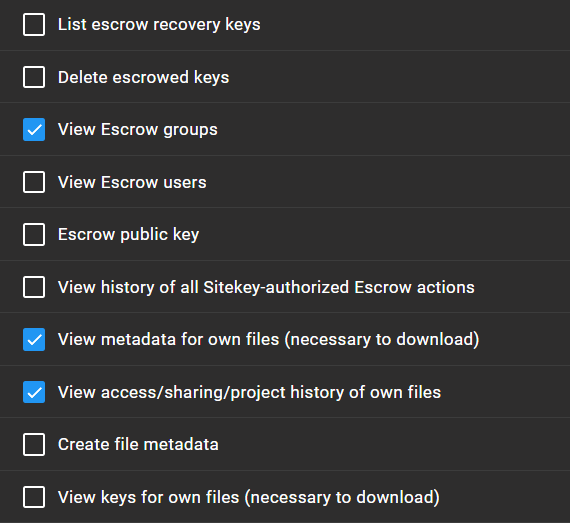
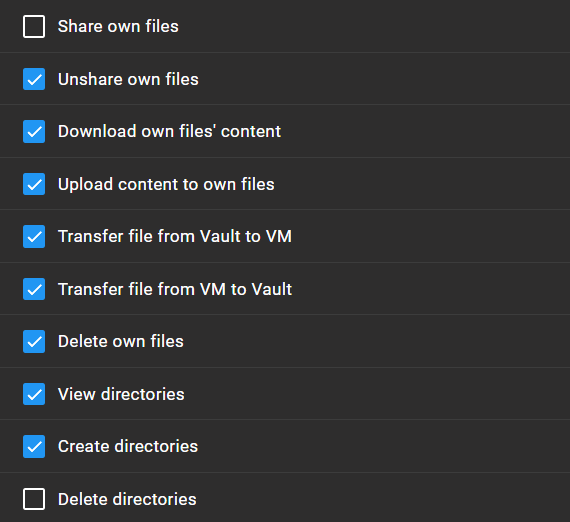
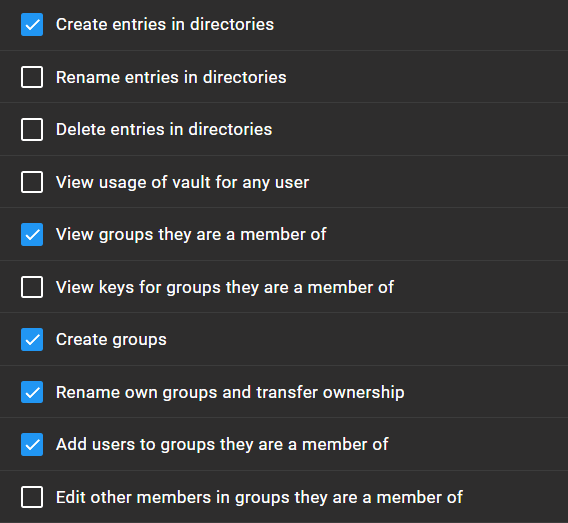
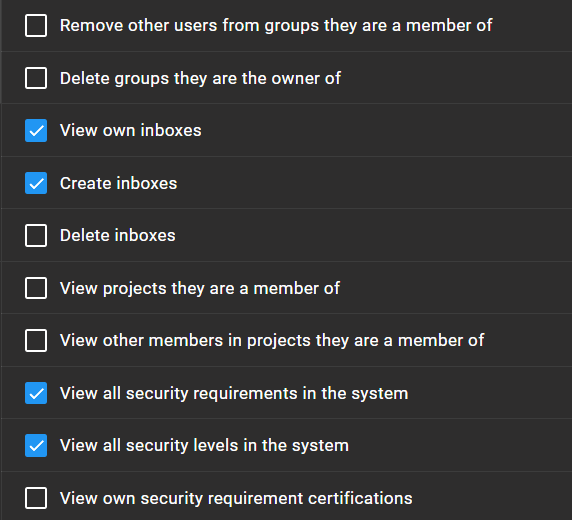
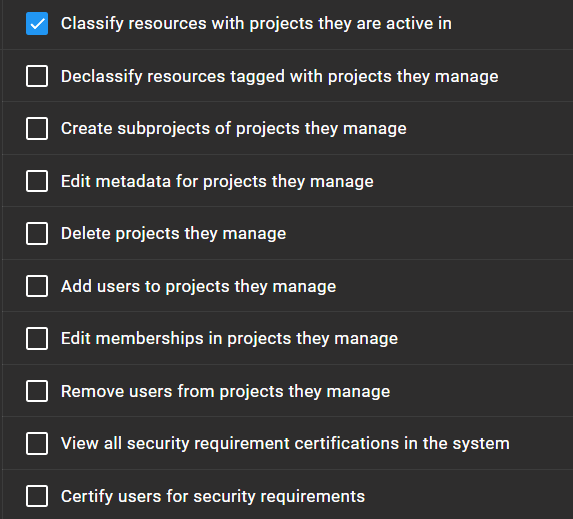
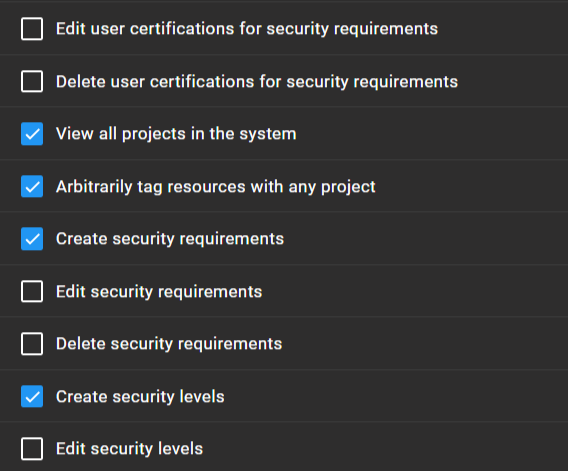
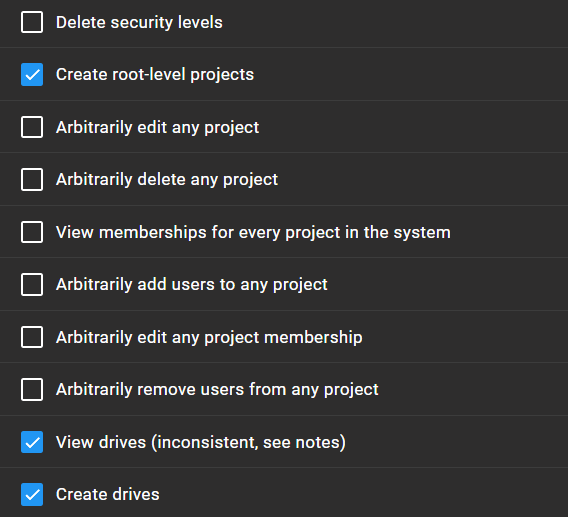
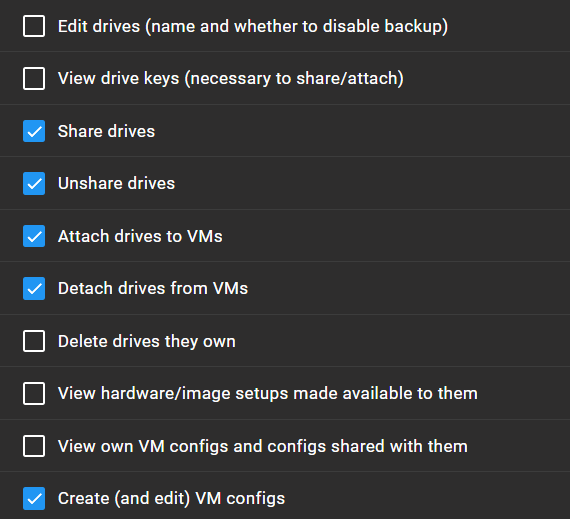
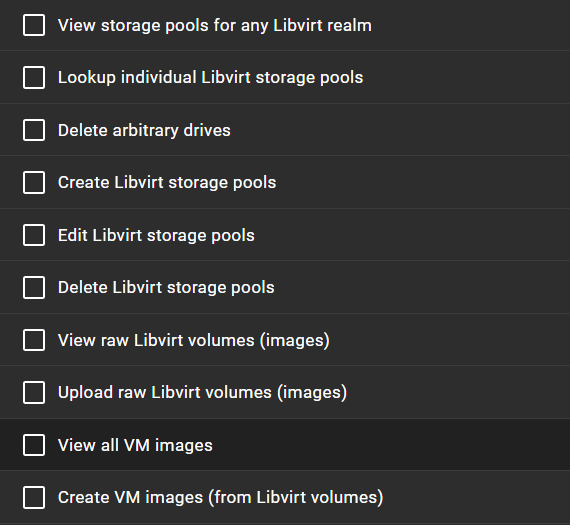
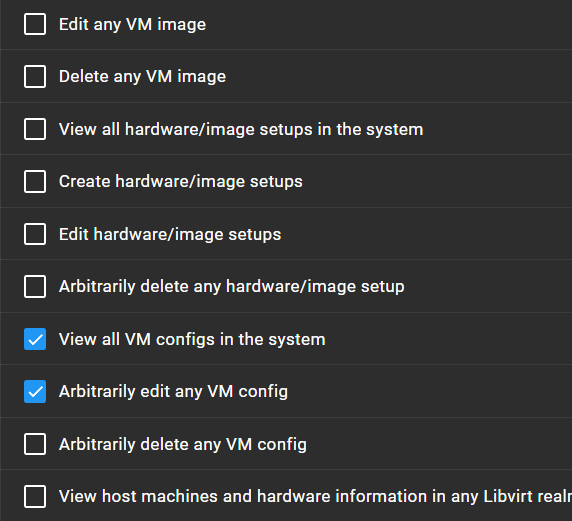
Granular Access Control
With 158 granular permissions, tiCrypt enables fine-grained control across users, projects, and system operations.
Organizations can combine permissions to enforce exact workflows aligned with their security requirements, operational structure, and compliance obligations.
Compliance
SSP Coverage (NIST 800-171 / CMMC Level 2)
tiCrypt provides a complete SSP blueprint (110 controls). Approximately 84 controls are platform-enforced (including hybrid controls where tiCrypt enforces the technical component). The remaining ~26 controls are organizational and require customer-specific policy edits (e.g., PE, AT, PS, and policy-driven areas).
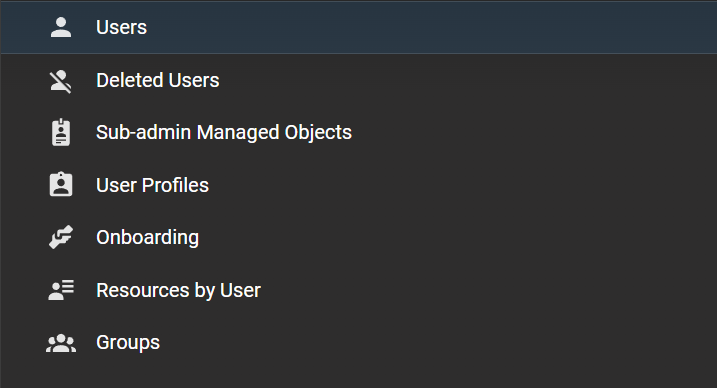
Management
Unified System Management
tiCrypt brings administrative controls, user management, projects, virtual machines, Slurm resources, escrow workflows, and system settings into a single, integrated control surface.
Each domain remains logically separated while managed through one unified interface.
Your Data Is Restricted. Your Workflows Shouldn't Be
One platform for encrypted storage, secure virtual machines, and CMMC/NIST compliant batch processing. Purpose-built for the most demanding security requirements without sacrificing the workflows you depend on.
End-to-End Encryption by Design
tiCrypt provides end-to-end encryption for file access, sharing, and processing, with a security model built on public-key cryptography.
- Per-user cryptographic key pairs
- Administrators cannot access user data
- Private keys never leave the client
- Secure key recovery with multi-party approval
What Our Customers Say About tiCrypt
Why tiCrypt?
tiCrypt is a single-stack solution designed for secure, compliance-ready data processing at scale.
tiCrypt vs Traditional In-House Solutions
A side-by-side comparison highlighting operational, security, and compliance differences.